Take a second and answer this seemingly straightforward question – how many passwords do you have? Not so easy to count, is it?
Approximately 81% of confirmed data breaches are due to weak or stolen passwords. Make sure your password is strong and unique!
In this article, we dive into brute force attacks — what they are, how hackers are using them, and prevention techniques.
What is a Brute Force Attack
A brute force attack is among the simplest and least sophisticated hacking methods. As the name implies, brute force attacks are far from subtle. The theory behind such an attack is that if you take an infinite number of attempts to guess a password, you are bound to be right eventually.
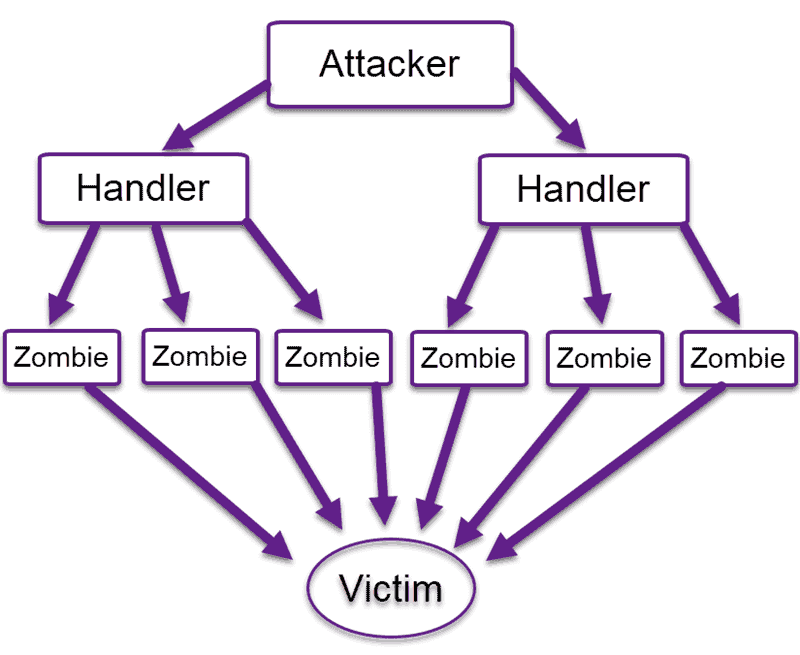
The attacker aims to forcefully gain access to a user account by attempting to guess the username/email and password. Usually, the motive behind it is to use the breached account to execute a large-scale attack, steal sensitive data, shut down the system, or a combination of the three.
Creating code that executes this type of attack doesn’t take much imagination or knowledge, and there are even widely available automated tools that submit several thousand password attempts per second.
How to Identify Brute Force Attacks
A brute force attack is easy to identify and investigate. You can detect them by looking into your Apache access log or Linux log files. The attack will leave a series of unsuccessful login attempts, as seen below:
Sep 21 20:10:10 host proftpd[25197]: yourserver (usersip[usersip]) - USER theusername (Login failed): Incorrect password.Does Locking-Out Accounts Work?
Locking out accounts after a certain number of incorrect password attempts is a common practice of dealing with brute force attempts. Unfortunately, that alone is not always sufficient.
Hackers can launch wide-scale attacks by trying a single password on several thousand servers. As opposed to attempting many passwords on a single server, this method does not trigger the account lockout, and it cleverly bypasses this defensive mechanism.
For example, if a server were under attack frequently, several hundred user accounts could be locked-out constantly. Your server would be easy prey for denial-of-service. Be proactive to detect and stop DDoS attacks.
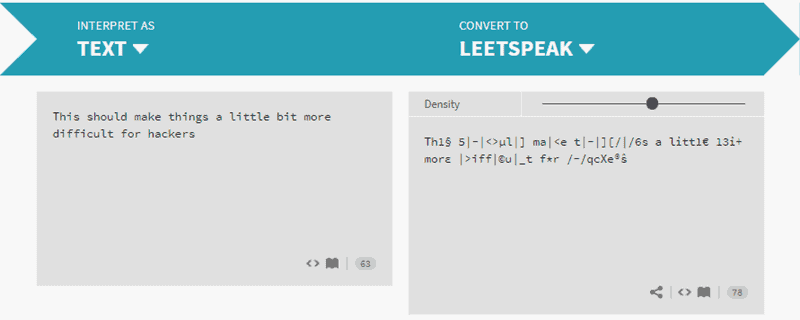
Does Using “LEET-speak” Help?
“Leetspeak” is an internet language that encodes any text by translating into ASCII characters.
For some time, Leetspeak was an effective way of adding another “security layer” to your password management. However, hackers have caught on and started using dictionaries that substitute letters with common Leet characters. The same goes for other common encrypting methods, such as SHA-1.
Brute Force Attack Prevention Techniques
There are many methods to stop or prevent brute force attacks.
The most obvious is a strong password policy. Each web application or public server should enforce the use of strong passwords. For example, standard user accounts should have at least eight letters, a number, uppercase and lowercase letters, and a special character. Moreover, servers should require frequent password changes.
Let’s investigate other ways to prevent a brute force attack.
- Limit failed login attempts
- Make the root user inaccessible via SSH by editing the sshd_config file
- Don’t use a default port, edit the port line in your sshd_configfile
- Use Captcha
- Limit logins to a specified IP address or range
- Two factor authentication
- Unique login URLs
- Monitor server logs

1. Account Lockouts After Failed Attempts
As stated above, implementing an account lockout after several unsuccessful login attempts is ineffective as it makes your server easy prey for denial-of-service attacks. However, if performed with progressive delays, this method becomes much more effective.
Account lockouts with progressive delays lock an account only for a set amount of time after a designated number of unsuccessful login attempts. This means that automated brute force attack tools will not be as useful. Additionally, admins will not have to deal with unlocking several hundred accounts every 10 minutes or so.
2. Make the Root User Inaccessible via SSH
SSH brute force attempts are often carried out on the root user of a server. Make sure to make the root user inaccessible via SSH by editing the sshd_config file. Set the ‘DenyUsers root’ and ‘PermitRootLogin no’ options.
3. Modify the Default Port
Most automated SSH attacks are attempted on the default port 22. So, running sshd on a different port could prove to be a useful way of dealing with brute force attacks.
To switch to a non-standard port, edit the port line in your sshd_config file.
4. Use CAPTCHA
We all got used to seeing CAPTCHA on the internet. Nobody likes trying to make sense of something that looks like it’s been scribbled by a two-year-old, but tools such as CAPTCHA render automated bots ineffective.
That single requirement to enter a word, or the number of cats on a generated image, is highly effective against bots, even though hackers have started using optical character recognition tools to get past this safety mechanism.
Bear in mind that the use of tools such as CAPTCHA negatively impacts the user experience.
5. Limit Logins to a Specified IP Address or Range
If you allow access only from a designated IP address or range, brute force attackers will need to work hard to overcome that obstacle and forcefully gain access.
It is like placing a security perimeter around your most precious data, and everyone who doesn’t originate from the right IP address is not allowed access.
You can set this up by scoping a remote access port to a static IP address. If you don’t have a static IP address, you can configure a VPN instead. One downside is that this might not be appropriate for every use case.
6. Employ 2-Factor Authentication (2FA)
Two-factor authentication is considered by many to be the first line of defense against brute force attacks. Implementing such a solution greatly reduces the risk of a potential data breach.
The great thing about 2FA is that password alone is not enough. Even if an attacker cracks the password, they would have to have access to your smartphone or email client. Very persistent attackers might try to overcome that obstacle, but most will turn around and search for an easier target.
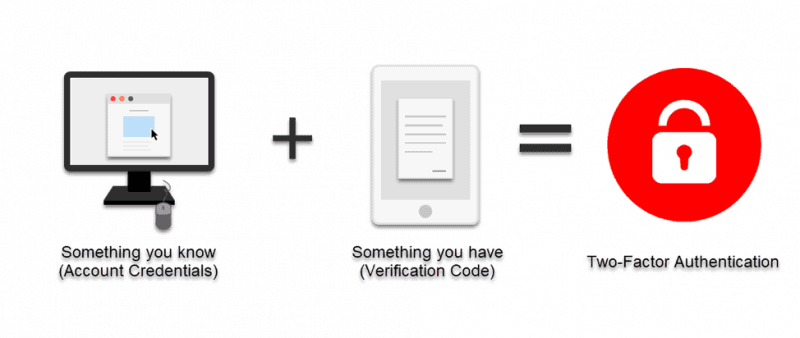
Note: Two-factor authentication is very effective against many types of attacks, including keylogger attacks. Many security guidelines stipulate the use of 2FA (e.g., HIPAA and PCI), and government agencies, such as FBI, require it for off-site logins. If you are using WordPress, learn here how to set up two-factor authentication for WordPress.
7. Use Unique Login URLs
Create unique login URLs for different user groups. This will not stop a brute force attack, but introducing that additional variable makes things a bit more challenging and time-consuming for an attacker.
8. Monitor Your Server Logs
Be sure to analyze your log files diligently. Admins know that log files are essential for maintaining a system.
Log management applications, such as Logwatch, can help you perform daily check-ups and can auto-generate daily reports.
Start Active Prevention & Protection From Brute Force Attacks Today
A skilled and persistent attacker will always find a way to eventually break-in.
Nonetheless, implementing a combination of the methods outlined above minimizes the chances of you becoming a victim of a brute force attack. Brute force attackers like easy prey, and are most likely to turn away and search for another target if you throw a wrench in their works.